Cumberlands Security Concerns and Mitigation Strategies Paper
Assignment Requirements
You are provided a handout to do this assignment.
Tasks
Identify a networked technology you use at home, at work, or as a personal convenience. Research and identify three potential threats to endpoint security of the device, and detail a mitigation mechanism for each threat. Also explain why your mitigation strategies would work. Submit the report to your instructor.
Required Resources
- Textbook
- Internet
- Handouts:
- Security Concerns and Mitigation Strategies
- Hosts
- RS Assignment 3 Security Concerns and Mitigation Strategies Template.docx (YOU MUST USE THIS TEMPLATE TO GET FULL CREDIT)
Submission Requirements
- Format: Microsoft Word
- Font: Arial, Size 12, Double-Space
- Citation Style: APA
- Length: 2–2 pages
- Spelling & Grammar count
Self-Assessment Checklist
- I identified at least one personally significant networked technology.
- I researched and identified three appropriate threats associated with the technology.
- I provided a mitigation strategy for each identified threat.
- I explained why my mitigation strategies would work.
Do you need a similar assignment done for you from scratch? We have qualified writers to help you. We assure you an A+ quality paper that is free from plagiarism. Order now for an Amazing Discount!
Use Discount Code "Newclient" for a 15% Discount!
NB: We do not resell papers. Upon ordering, we do an original paper exclusively for you.


 We are an online Writing Agency that specializes in writing and editing nursing essays and academic assignments..
We are an online Writing Agency that specializes in writing and editing nursing essays and academic assignments..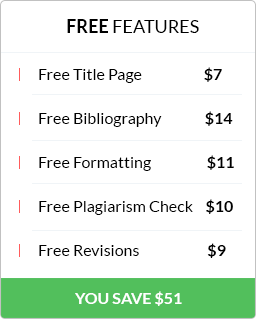
 Have any questions? Talk to us…
Have any questions? Talk to us…