theories security
ResearchPaperWriters.com has established itself as the best academic writing website through a combination of well-furnished writers, highly-rated custom research paper writing services, top-level writers, discounts, punctual delivery, and 24/7 support. These facets come together to create a platform that not only meets but often exceeds the academic writing needs of its clients. Whether you are a student grappling with tight deadlines or a researcher in need of in-depth, well-researched papers, ResearchPaperWriters.com is the pinnacle of academic writing excellence, ready to provide you with top-tier services and exceptional results. At the core of ResearchPaperWriters.com’s success are its well-furnished writers. The platform prides itself on the caliber of its writers, who are highly qualified professionals with expertise in various academic fields. These writers have a deep understanding of the intricacies and requirements of different academic disciplines, ensuring that each project is handled with the utmost care and competence. Their proficiency in conducting thorough research and crafting well-structured, academically rigorous papers is the cornerstone of the website’s success.
Technical Paper: Risk Assessment
Due Week 10 and worth 160 points

Global Finance, Inc. Network Diagram
Above is the Global Finance, Inc. (GFI) network diagram. A hypothetical company, GFI has grown rapidly this past year and implemented a number of network devices as displayed in the diagram. The company invested in the network and designed it to be fault tolerant and resilient from any network failures. However, although the company’s financial status has matured and its network has expanded at a rapid pace, its overall network security posture has not kept up with the company growth.
GFI’s network has historically been fairly stable, and the company has not experienced many full scale network outages. GFI has hired three (3) network engineers to keep up with the network growth, as well as the bandwidth demand by the company employees and the clients. However, the company has not hired any security personnel who can take care of the operational security responsibility.
The trusted computing base (TCB) internal network within the Global Finance, Inc. Network Diagram hosts the company’s mission critical systems that are vital to the company’s operations that also affect the overall financial situation. The Oracle database and email systems are among the most intensively used application servers in the company. GFI cannot afford system or network outages, as its cash flow and financial systems heavily depend on the network stability and availability. GFI has experienced DoS network attacks twice this year, and its Oracle database and email servers had been down for a total of one (1) week as a result. The recovery process required GFI to utilize $25,000 to restore its operations to the normal operating baseline. GFI estimated the loss from these network attacks at more than $1,000,000, as well as lost customer confidence.
Write an eight to ten (8-10) page formal risk assessment proposal in which you:
- Describe the company network, interconnection, and communication environment.
- Assess risk based on the GFI, Inc. network diagram scenario. Note: Your risk assessment should cover all the necessary details for your client, GFI Inc., to understand the risk factors of the organization and risk posture of the current environment. The company management will utilize this risk assessment to determine what actions to take; therefore, it must be comprehensive for the business leaders to make data-driven decisions.
- Defend your assumptions where pertinent information from the scenario isn’t available.
- Ascertain apparent security vulnerabilities, and analyze at least three (3) such vulnerabilities. Such analysis should entertain the possibility of faulty network design. Recommend mitigation processes and procedures for each of the identified vulnerabilities.
- Justify your cryptography recommendations, based on security concerns and requirements, data-driven decision-making, and objective opinions.
- Examine whether your risk assessment methodology is quantitative, qualitative, or a combination of these, and discuss the main reasons why you believe that the methodology that you utilized was the most appropriate.
- Explain the way in which you would present your findings and assessment to the company’s management and thus facilitate security buy-in and concentration.
- Using Microsoft Visio or its open source equivalent, redraw the CFI diagram, depicted as a secure and risk-mitigating model. Note: The graphically depicted solution is not included in the required page length.
- Use at least three (3) quality resources in this assignment. Note: Wikipedia and similar Websites do not qualify as quality resources.
Your assignment must follow these formatting requirements:
- Be typed, double spaced, using Times New Roman font (size 12), with one-inch margins on all sides; citations and references must follow APA or school-specific format. Check with your professor for any additional instructions.
- Include a cover page containing the title of the assignment, the student’s name, the professor’s name, the course title, and the date. The cover page and the reference page are not included in the required assignment page length.
- Include charts or diagrams created in Visio or an open source alternative such as Dia. The completed diagrams / charts must be imported into the Word document before the paper is submitted.
The specific course learning outcomes associated with this assignment are:
- Evaluate an organization’s security policies and risk management procedures, and its ability to provide security countermeasures.
- Analyze the methods of managing, controlling, and mitigating security risks and vulnerabilities.
- Explain access control methods and attacks.
- Describe the details and the importance of application security models and their implementation from a management perspective.
- Evaluate and explain from a management perspective the industry-standard equipment, tools, and technologies organizations can employ to mitigate risks and thwart both internal and external attacks.
- Use technology and information resources to research issues in security management.
- Write clearly and concisely about the theories of security management using proper writing mechanics and technical style conventions.
ResearchPaperWriters.com’s pool of top-level writers is a testament to its dedication to quality. The website carefully selects its writers, ensuring they possess advanced degrees and a proven track record of academic writing excellence. This commitment to excellence translates into papers that not only meet but often exceed the expectations of clients, contributing to the platform’s well-deserved reputation as the best in the business. Affordability is another key aspect that makes ResearchPaperWriters.com the best academic writing website. The platform understands the financial constraints that students often face and strives to provide cost-effective solutions. Clients can benefit from discounts and bonuses that help make these high-quality services accessible. These financial incentives, in conjunction with exceptional writing quality, make ResearchPaperWriters.com the go-to choice for academic assistance.
Do you need a similar assignment done for you from scratch? We have qualified writers to help you. We assure you an A+ quality paper that is free from plagiarism. Order now for an Amazing Discount!
Use Discount Code "Newclient" for a 15% Discount!
NB: We do not resell papers. Upon ordering, we do an original paper exclusively for you.


 We are an online Writing Agency that specializes in writing and editing nursing essays and academic assignments..
We are an online Writing Agency that specializes in writing and editing nursing essays and academic assignments..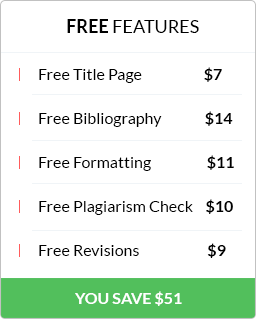
 Have any questions? Talk to us…
Have any questions? Talk to us…